If there’s one thing that frustrates employees, it’s working with outdated and inefficient equipment, or learning to adapt to unfamiliar equipment. Remember the last time you had to fight the technology instead of working on your projects? To many organizations, this topic is a daily conversation among employees.
An alternative to controlling all corporate devices in a rigid structure is allowing your employees to bring their own devices (BYOD) to work and access business applications and corporate data from anywhere. For many organizations, especially small firms that are more agile and less encumbered by rigid systems, the adoption of BYOD policies is changing the workplace for the better.
Happy users work harder
With a BYOD policy in place, your employees can choose the tools and devices they prefer, making work more enjoyable and productive with their favorite devices and productivity applications.
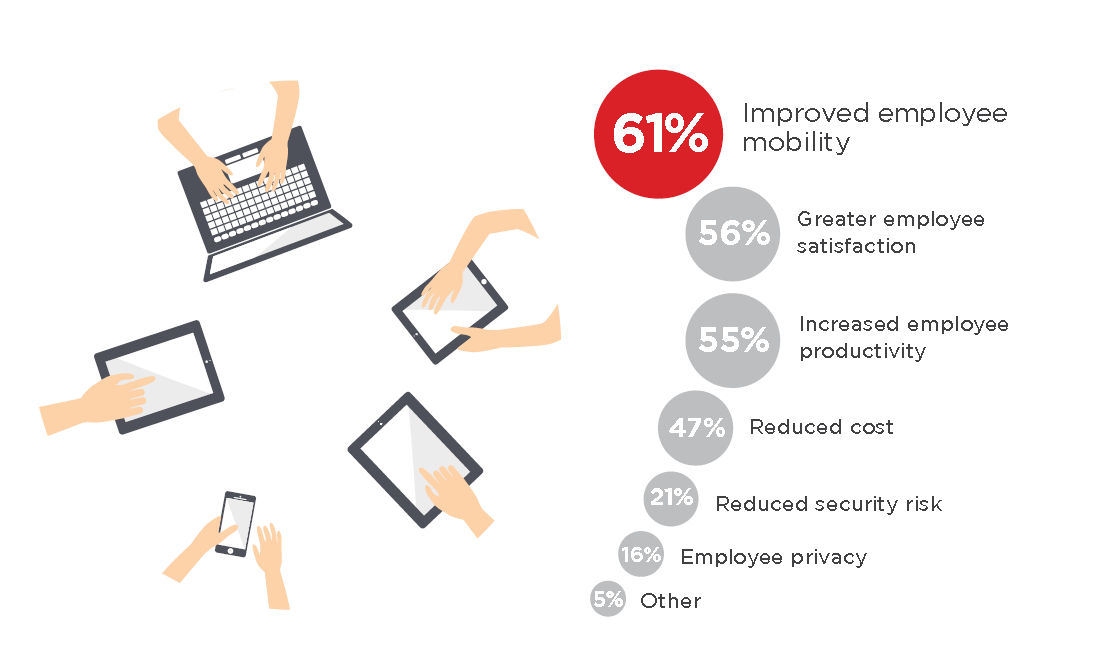
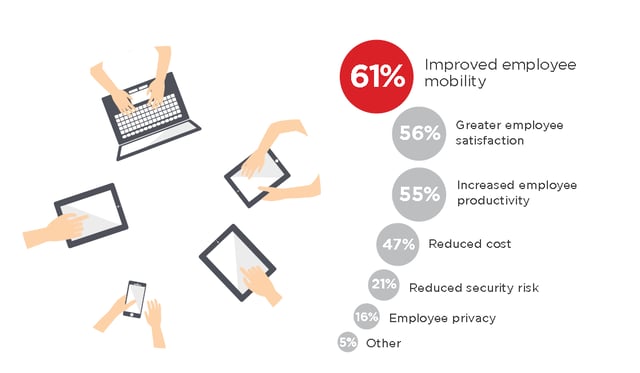
According to the Crowd Research Partner’s BYOD Spotlight Report, the top three drivers of BYOD are improved mobility (61 percent), greater satisfaction (56 percent), and increased productivity (55 percent). These employee-related benefits are even considered more important than reduced costs (47 percent).
Embracing the BYOD approach will lead to happy, productive, and accomplished teams.
Companies spend less on devices
From big capital expenditures on data centers to employees’ request for a new phone or computer, IT has been an expensive cost center for companies. Requiring long-term contracts with vendors and suppliers, and refreshing hardware in the next recycling period, or when that equipment crashed.
Owning the hardware also required additional services like computer cabling, external hard drives, mobile data, and so on. IT controlled the entire IT ecosystem and had to finance every element of it.
With the BYOD approach, companies can save on costs while increasing employee satisfaction and productivity. The company can provide predictable stipends for user equipment and IT only need focus on providing a secure access method and ecosystem. And money that was previously spent on IT equipment can now be invested in cutting-edge technology that can drive business values.
Read more about how the Cloud is transforming IT from CapEx to OpEx and shedding the "cost center" label
Risks to consider
It’s no wonder that BYOD is attractive to both employees and employers. However, there are a number of downsides that make many companies hesitate to adopt such approach.
From the user standpoint, an incomplete BYOD policy would raise serious privacy and user experience issues, for example:
- Users have multiple logins to different systems, both personally and professionally;
- There is no access to Windows-based applications on Mac devices;
- Company might scan their personal emails and data stored on the devices;
From the organizational standpoint, the biggest concerns are involved with data security. Such risks include:
- Unauthorized access to company data and systems;
- Users download unsafe apps, malware, and other infectious software;
- Lost and stolen devices;
- Network attacks via unsecured WiFi
Beyond security concerns, IT also has to deal with multi-device management, which would require a different procedure to the following tasks:
- Ensuring up-to-date security software on any device
- Regulation compliance
- Integration with existing network and application stack
If your business has operated without the BYOD approach for several years, you’re probably thinking “Why bother?” With the growing use of cloud services, in particular cloud hosted desktops and applications, you can employ a successful BYOD policy – cutting costs while delivering a seamless user experience and keeping everything secure.
Plan your BYOD approach in the right way
A proper BYOD policy does not necessarily mean that IT departments lose control over applications and programs. With the use of multiple devices and operating systems, IT needs to take steps to maintain control over corporate data and applications, which is possible if planned correctly.
A complete BYOD approach requires IT to provide:
- Protection: We need solutions that not only detects threats but also remediates them based on corporate policy;
- Integration: We need a solution that integrates with our existing network, end-point, or application platforms;
- Visibility: We need to see and control all end-user access, affected devices, and the types of threats;
There is no need for IT to come up with the solutions on their own. You can choose from many solutions to assist your BYOD policy, such as Microsoft Intune for mobile device management, Virtual Private Network (VPN) for data and device encryption, or a cloud workspace solution that provides native desktop or application experience in the cloud with corporate-level security and industry compliance.
To minimize risks associated with BYOD, you must start educating employees on BYOD policy security needs as soon as possible. These education topics can include:
- Physical device use: general security requirements for mobile devices and authentication (password/PIN), and the rights to monitor, manage, and whip data by IT departments;
- Mobile software use: authorized access to business applications and data;
- Network security: storage/transmission encryption requirements;
Tags: Managed Service Provider